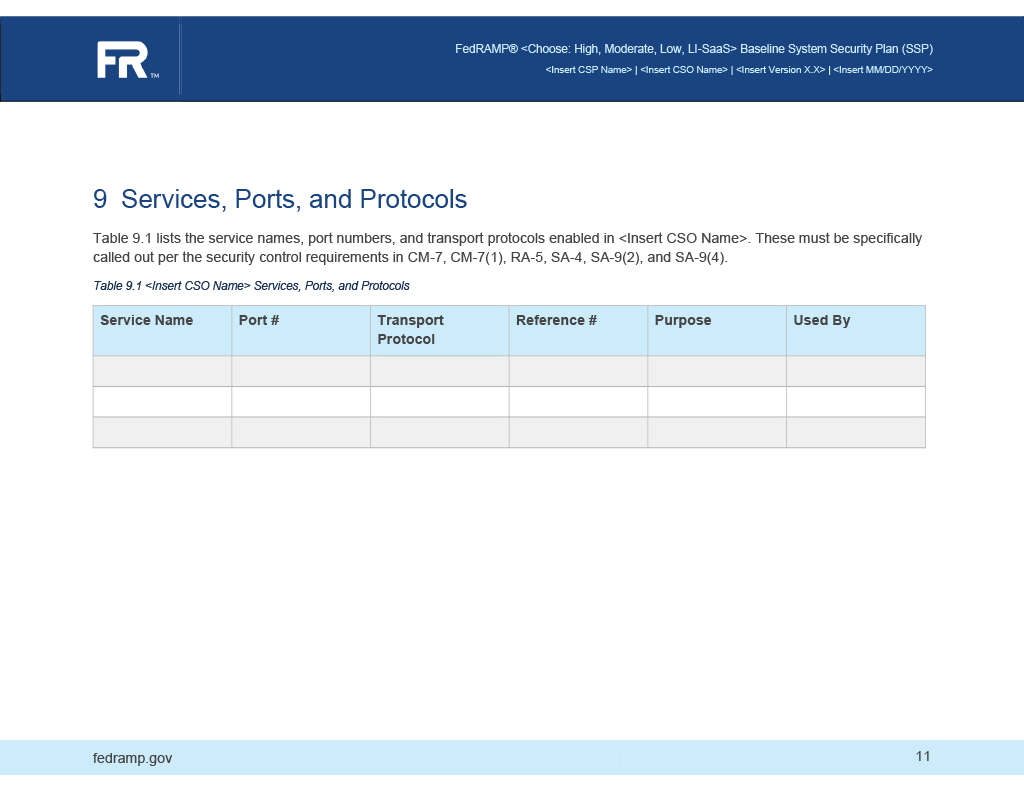
9. Services, Ports and Protocols
Entries in the services, ports, and protocols table are represented as component assemblies, with the component-type flag set to "service". Use a protocol assembly for each protocol associated with the service. For a single port, set the port-range start flag and end flag to the same value.
OSCAL Representation
system-security-plan:
uuid: 11111111-2222-4000-8000-000000000000
system-implementation:
components:
- uuid: 11111111-2222-4000-8000-009000500004
type: service
title: API Service
description: 'A service offered by this system to external systems, such as
an API. As a result, communication crosses the boundary.
Describe the service and what it is used for.'
props:
- name: implementation-point
value: internal
- name: public
value: 'yes'
- name: information-type
ns: http://fedramp.gov/ns/oscal
value: C.3.5.1
class: incoming
- name: information-type
ns: http://fedramp.gov/ns/oscal
value: C.3.5.8
class: outgoing
- name: connection-security
ns: http://fedramp.gov/ns/oscal
value: tls-1.3
- name: authentication-method
ns: http://fedramp.gov/ns/oscal
value: 'yes'
- name: nature-of-agreement
ns: http://fedramp.gov/ns/oscal
value: other
- name: allows-authenticated-scan
value: 'no'
- name: scan-type
ns: http://fedramp.gov/ns/oscal
value: infrastructure
links:
- href: '#11111111-2222-4000-8000-009000100003'
rel: used-by
- href: '#11111111-2222-4000-8000-009000100004'
rel: used-by
- href: '#11111111-2222-4000-8000-001000000048'
rel: poam-item
resource-fragment: 11111111-3333-4000-8000-000000000004
- href: https://api.example.com/v1
rel: api
status:
state: operational
responsible-roles:
- role-id: administrator
props:
- name: privilege-uuid
ns: http://fedramp.gov/ns/oscal
value: 11111111-2222-4000-8000-008000000004
party-uuids:
- 11111111-2222-4000-8000-004000000010
- 11111111-2222-4000-8000-004000000011
- 11111111-2222-4000-8000-004000000012
- role-id: provider
party-uuids:
- 11111111-2222-4000-8000-004000000001
protocols:
- uuid: 11111111-2222-4000-8000-010000000002
name: tls
title: API Service
port-ranges:
- start: '443'
end: '443'
transport: TCP
To represent Network Services and Ports within an OSCAL System Security Plan, the data is organized under the system-implementation section, specifically categorized by components where the type is defined as a service.
The mapping for each service entry includes the following technical details:
- Service Identity: Each entry starts with a
titlethat identifies the specific service or application name (e.g., "HTTPS" or "SSH"). - Protocol Configuration: The specific network
protocolname (such as TCP or UDP) is identified to define how the service communicates. - Port Management: Detailed port information is captured within a
port-range, specifying the exactstartandendvalues. This also includes thetransportlayer designation to ensure the specific communication path is fully defined. - Functional Justification: A dedicated
purposefield provides the business or technical rationale for why the service is required within the system boundary. - Component Relationships: The model tracks which internal system elements are utilizing the service by linking to the
titleof other defined components via their unique identifiers (UUIDs).
For systems with multiple services, each is documented as an individual service component, with the ability to define multiple protocols and port ranges within each entry to maintain a complete and granular inventory.
