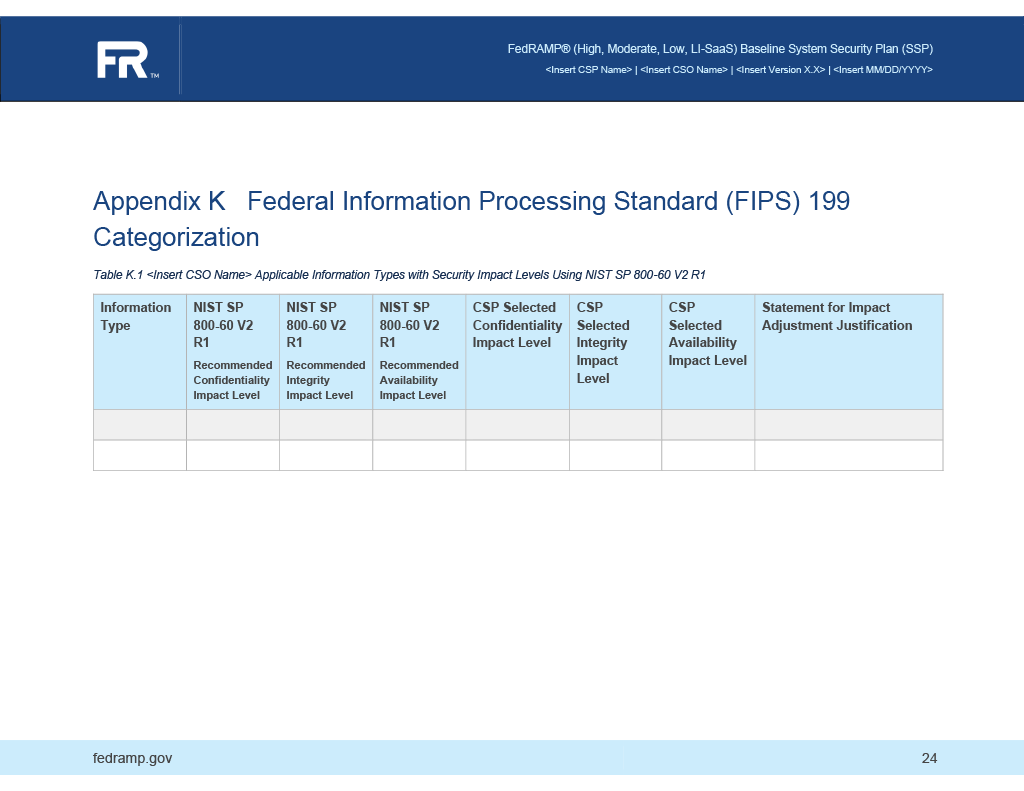
Appendix K: FIPS-199 Worksheet
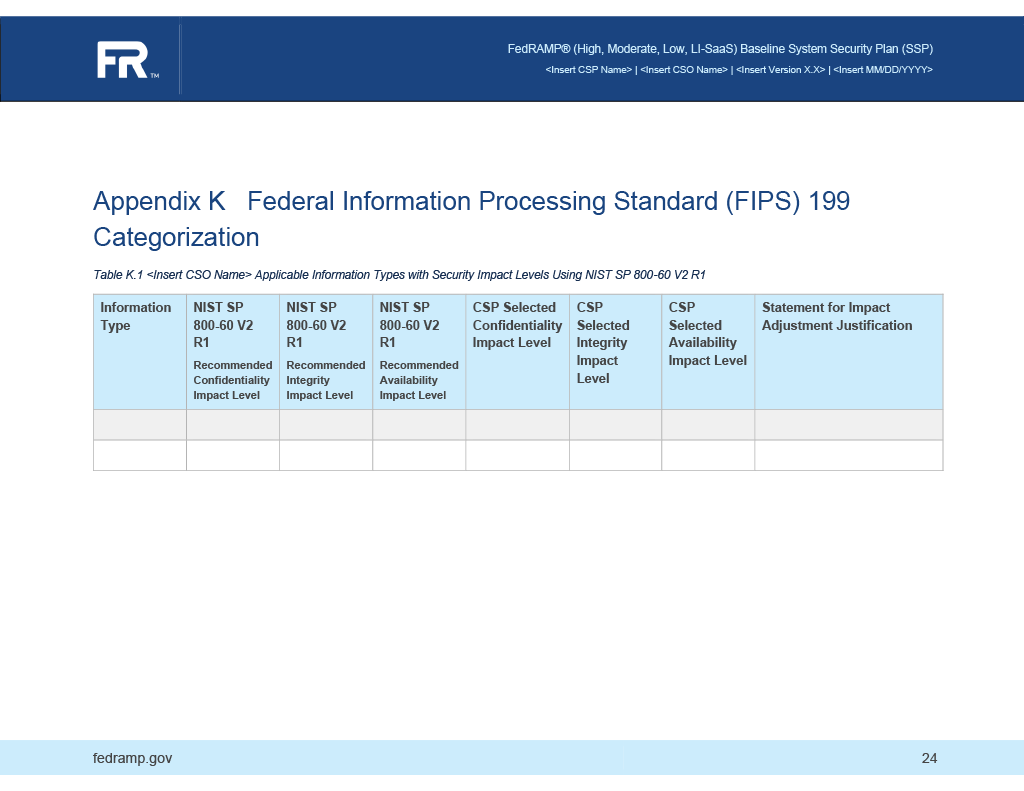
The FIPS-199 Categorization inworksheet theis FedRAMPan SSPinventory template,of illustratedinformation types in the figuresystem, below,based on NIST SP 800-60 Volume 2.
- Create one entry under
information-typesfor each information type. - For each information type:
- Assign a
uuid - Assign the NIST SP 800-63 information type name to the
title descriptionisexpressedathroughrequired OSCAL field that is not acknowledged by FedRAMP. Consider offering context or citing 800-60.- The
categorizationsarray should have one entry that includes:systemset to "http://doi.org/10.6028/NIST.SP.800-60v2r1"- the
information-type-idsarraqy should have one entry- Use the
followingNISTcoreSPOSCAL800-60property.invormation type ID - Exactly match the case as it appears in 800-60. (e.g.,
C.2.3.1orD.15.5)
- Use the
- The
confidentiality-impactmust have:- a
basefield with the value defined in 800-60. - a
selectedfield with the value selected by the CSP. - If the value in
selecteddoes not match the value inbase, useadjustment-justificationto capture the "Statement for Impact Adjustment Justification" baseandselectedvalues must be one offips-199-low,fips-199-moderateorfips-199-high
- a
integrity-impact andavailability-impactare treated the same asconfidentiality-impact` above.
- Assign a
Other information types or categorizations may be present if the SSP also represents compliance with other frameworks; however, the US Government must operate under NIST RMF and will only recognize the NIST SP 800-60 types.
OSCAL Representation
system-security-plan:
system-characteristics:
system-name:information:
System'sinformation-types:
Full- uuid: 11111111-2222-4000-8000-006000000001
title: Information Type Name
system-name-short:description: System'sA Shortdescription Nameof orthe Acronyminformation.
system-categorizations:
- system: http://doi.org/10.6028/NIST.SP.800-60v2r1
information-type-ids:
- identifier-type:C.2.4.1
http://fedramp.govconfidentiality-impact:
id: F00000000
security-sensitivity-level:base: fips-199-moderate
selected: fips-199-moderate
adjustment-justification: Required if the base and selected values do not
match.
integrity-impact:
base: fips-199-moderate
selected: fips-199-low
adjustment-justification: Required if the base and selected values do not
match.
availability-impact:
base: fips-199-moderate
selected: fips-199-moderate
adjustment-justification: Required if the base and selected values do not
match.
OSCAL Allowed Values
Reqired value for system:
- http://doi.org/10.6028/NIST.SP.800-60v2r1
Valid values for security-sensitivity-level:base and selected fields:
- fips-199-low
- fips-199-moderate
- fips-199-high
XPath Queries
System Sensitivity Level:
/*/system-characteristics/security-sensitivity-level
Digital Identity Level (DIL) Determination
The digital identity level identified in the FedRAMP SSP template document, illustrated in the figure below, isexpressed through the following core OSCAL properties.
system-security-plan:
system-characteristics:
props:
- name: identity-assurance-level
value: 1
- name: authenticator-assurance-level
value: 1
- name: federation-assurance-level
value: 1
OSCAL Allowed Values
Valid IAL, AAL, and FAL values (as defined by NIST SP 800-63):
123
System Sensitivity Level
In addition to the security-sensitivity-level, you must supply impact levels for each security objective: confidentiality, integrity, and availability.
Each objective value corresponds to the highest impact level for that objective across all information types. For example, if two information types are described, one with a confidentiality impact level of fips-199-low and another with fips-199-moderate, the resulting value for security-objective-confidentiality must be fips-199-moderate.
The overall security-sensitivity-level must reflect the highest impact level across all three objectives.
OSCAL Representation
system-security-plan:
system-characteristics:
security-impact-level:
security-objective-confidentiality: fips-199-moderate
security-objective-integrity: fips-199-moderate
security-objective-availability: fips-199-moderate
NOTES:
The identified System Sensitivity Level governs which FedRAMP baseline applies.The system sensitivity level should match the highest security impact level for the system’s confidentiality, integrity, and availability objectives, but in rare exceptions (e.g., when the AO specifies and overrides the expected security sensitivity level), they may differ.
