Appendix Q: Cryptographic Modules
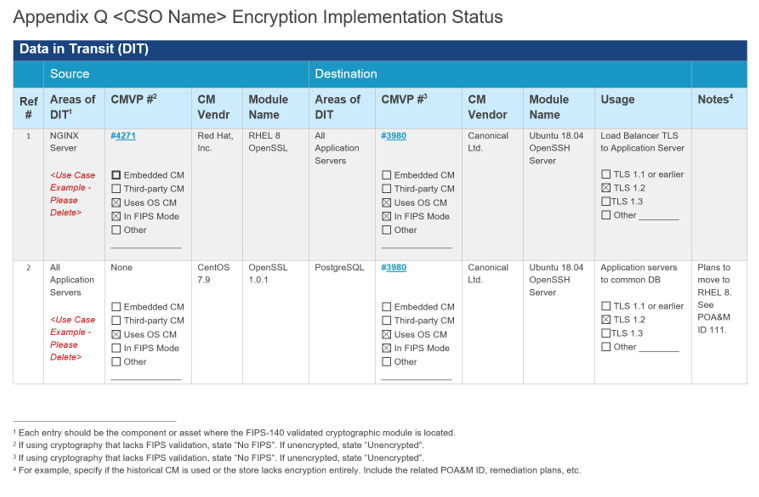
Cryptographic Modules Implemented for Data-in-Transit (DIT)
This page needs work:
- The examples needs to be converted to YAML
- A description of the YAML constructs needs to be provided
OSCAL's component model treats independent validation of products and services as if that validation were a separate component. This means when using components with FIPS 140 validated cryptographic modules, there must be two component assemblies:
-
The Validation Definition: A component that provides details about the validation.
-
The Product Definition: A component that describes the hardware or software product.
The validation definition is a component that provides details about the independent validation. Its type must have a value of "validation". In the case of FIPS 140 validation, this must include a link field with a rel value set to "validation-details". This link must point to the cryptographic module's entry in the NIST Computer Security Resource Center (CSRC) Cryptographic Module Validation Program Database.
The product definition is a product with a cryptographic module. It must contain all of the typical component information suitable for reference by inventory-items and control statements. It must also include a link field with a rel value set to "validation" and an href value containing a URI fragment. The fragment must start with a hashtag (#) and include the UUID value of the validation component. This links the two together.
Component Representation: Example Product with FIPS 140-2 Validation
system-security-plan:
uuid: 11111111-2222-4000-8000-000000000000
system-implementation:
components:
- uuid: 11111111-2222-4000-8000-009000300003
type: software
title: OpenSSL
description: 'Provide a description and any pertinent note regarding the use
of this CM.
For data-at-rest modules, describe type of encryption implemented (e.g., full
disk, file, record-level, etc.)
Lastly, provide any supporting notes on FIPS status (e.g. historical) or lack
of FIPS compliance (e.g., Module in Process).'
props:
- name: asset-type
value: cryptographic-module
- name: version
value: 3.0.8
- name: vendor-name
ns: http://fedramp.gov/ns/oscal
value: OpenSSL FIPS Provider
- name: function
ns: http://fedramp.gov/ns/oscal
value: data-in-transit
remarks: Usage statement
links:
- href: '#11111111-2222-4000-8000-009001200002'
rel: validation
text: A link to the 3rd party validation information related to this cryptographic
module.
status:
state: operational
- uuid: 11111111-2222-4000-8000-009001200002
type: validation
title: OpenSSL FIPS 140-2 Validation
description: Describe any relevant information regarding this validation of
the CM.
props:
- name: asset-type
value: cryptographic-module
- name: validation-type
value: fips-140-2
- name: validation-reference
value: '4811'
status:
state: operational
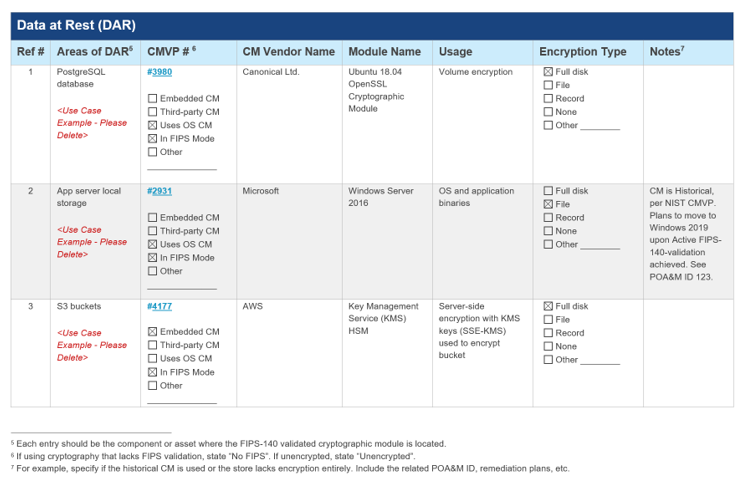
Cryptographic Modules Implemented for Data-at-Rest (DAR)
The approach is the same as in the cryptographic module data-in-transit section.
Component Representation: Example Product with FIPS 140-2 Validation
system-security-plan:
uuid: 11111111-2222-4000-8000-000000000000
system-implementation:
components:
- uuid: 11111111-2222-4000-8000-009000300012
type: software
title: Database Row Encryption Module
description: Briefly describe the cryptographic module.
props:
- name: asset-type
value: cryptographic-module
- name: version
value: 1.2.3
- name: vendor-name
ns: http://fedramp.gov/ns/oscal
value: Databases-R-Us
- name: function
ns: http://fedramp.gov/ns/oscal
value: data-at-rest
remarks: Used to encrypt and decrypt rows in the database.
status:
state: operational
- uuid: 11111111-2222-4000-8000-009001200001
type: validation
title: Database Row Encryption Module (DREM)
description: Briefly describe the cryptographic module.
props:
- name: asset-type
value: cryptographic-module
- name: validation-type
value: fips-140-2
- name: validation-reference
value: '0000'
status:
state: operational