Control Response: Policies, Procedures, Plans, RoB, and Guides
TheMost firstFedRAMP-required controlattachments inderive eachtheir requirement from one or more NIST SP 800-53 controlcontrols.
familyWith an OSCAL SSP, the attachment is alinked policydirectly andfrom procedurethe control. TheseThis areis sometimeshow referedtools know which attachment satisfies each requirement.
| Control ID | Artifact to |
Expected |
|---|---|---|
Each -1 |
Policy | 1 |
Each -1 |
Procedure(s) | 1+ |
SA-5 (id=sa-5) |
Appendix |
1 |
PL-4 (id=pl-4) |
Rules of |
1 |
CP-2 id=cp-2) |
Information |
1 |
CM-9 id=cm-9) |
Configuration |
1 |
IR-8 id=ir-8) |
Incident
|
1 |
CA-7 (id=ca-7) |
Continuous Monitoring Plan | 1 |
SR-2 (id=sr-2) |
Supply Chain Risk Management Plan (SCRMP) | 1 |
Organization:Retrofit Policy and Procedure StatementsMVP
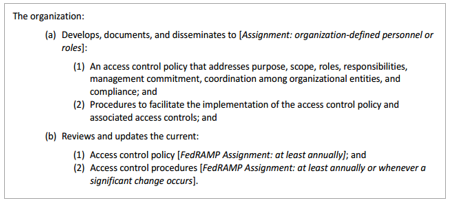
For eachRetrofit ofMVP, thesimply -1 controls, such as AC-1, there must be exactly four
statement assemblies: Part (a)(1), Part (a)(2), Part (b)(1), and Part
(b)(2).
Policy and Procedure Representation
<!-- system-implementation -->
<control-implementation>
<!-- cut -->
<implemented-requirement uuid="uuid-value" control-id="ac-1">
<statement statement-id="ac-1_smt.a.1"><!-- cut --></statement>
<statement statement-id="ac-1_smt.a.2"><!-- cut --></statement>
<statement statement-id="ac-1_smt.b.1"><!-- cut --></statement>
<statement statement-id="ac-1_smt.b.2"><!-- cut --></statement>
</implemented-requirement>
</control-implementation>
Response: Overview
Within each statement assembly, all responses must be provided within
one or more by-component assemblies. There must always beuse a componentlinks definedarray in the system-implementationimplemented-requirementsrepresenting the system as a whole
("THIS SYSTEM"), even if individual components are defined that
comprise the system. See the Working with Components sectionentry for moreeach information."-1" control.
system-security-plan:
control-implementation:
description: There is one control in this example. Follow this pattern for each
additional control.
implemented-requirements:
- uuid: 11111111-2222-4000-8000-012000010000
control-id: ac-1
links:
- href: ./AC_Policy.docx
rel: policy
media-type: application/docx
- href: ./AC_Procedure.docx
rel: procedure
media-type: application/docx
Normalized
AnFor OSCAL-basedRetrofit FedRAMP SSP should define individual components of the
system. Components are not just hardwareAdvanced, and software. Policies,
processes, FIPS 140 validation information, interconnections, services,
and underlying systems (leveraged authorizations) are all components.
With OSCAL, the content in the cell next to Part a must be broken down
into its individual components and responded to separately.
ForAttachParteachadocument- as
back-matter/resourcesentriesComponentCreate-componentsThisforSystemeach- document in
system-implementation/componentsDescribesAddhowimplemented-requirementspart/astatementsis/satisfiedby-componentsholistically,entryorforwhere the description does not fit with a defined component.each
system-security-plan:
Componentsystem-implementation:
components:
- Platformuuid: 11111111-2222-4000-8000-009000600001
Describestype: howpolicy
parttitle: a is satisfied by the platform.
Component - Web-Server
Describes how part a is satisfied by the web server.
Component - Process
Describes how part a is satisfied by an identified process within this organization.
Component - Inherited
Describes what is inherited from the underlying Infrastructure as a Service (IaaS) provider to satisfy part a.
For Part b
Component - This System
Describes how part b is satisfied holistically, or where the description does not fit with a defined component.
Component - Platform
Describes how part b is satisfied by the platform.
Component - Web-Server
Describes how part b is satisfied by the web server.
Component - Process
Describes how part b is satisfied by an identified process within this organization.
Component - Inherited
Describes what is inherited from the underlying Infrastructure as a Service (IaaS) provider to satisfy part b.
The following are examples.
Response: "This System" Component
There must always be a "This System" component in the SSP. This is used in several ways:
Holistic Overview: The SSP author may wish to provide a more
holistic overview of how several components work together, even if
details are provided individually in other by-component assemblies.
Catch-all: Any control response that does not cleanly align with
another system component may be described in the "This System"
component.
Legacy SSP Conversion: When converting a legacy SSP to OSCAL,
the legacy control response statements may initially be associated
with the "This System" component until the SSP author is able
to provide responses for individual components.
{{< figure src="/img/ssp-figure-38.png" title="SSP Template Security Control Response" alt="Figure illustrating how legacy SSP template control response is broad and should apply to the 'this-system' component in OSCAL." >}}
Representation
<system-implementation>
<!-- leveraged-authorization, user -->
<component uuid="uuid-value" type="this-system">
<title>This System</title>
<description>
<p>Description of the component.</p>
</description>
<status state="operational"/>
</component>
</system-implementation>
<control-implementation>
<!-- cut -->
<implemented-requirement uuid="uuid-value" control-id="ac-2">
<statement uuid="uuid-value" statement-id="ac-2_smt.a">
<by-component uuid="uuid-value" component-uuid="uuid-of-this-system-component">
<description>
<p>Describe how individual components are working together.</p>
<p>Describe how the system - as a whole - is satisfying this statement.</p>
<p>This can include policy, procedures, hardware, software, etc.</p>
</description>
</by-component>
</statement>
<!-- repeat statement assembly for statement part (b, c, etc.) as needed. -->
</implemented-requirement>
</control-implementation>
<!-- back-matter -->
NOTES:
Although the name of the component is "This System",
non-technical solutions may also be discussed here, such as policies
and procedures.
Linking to Artifacts
Any time policies, procedures, plans, and similar documentation are
cited in a control response, they must be linked.
For the legacy approach, when responding within the by-component
assembly for "this system", the link must be within the same by-component assembly where the artifact is cited.
{{< figure src="/img/ssp-figure-39.png" title="SSP Template Security Control Response" alt="Figure illustrating how legacy SSP template control response should link to the appropriate artifact." >}}
Representation: Legacy Approach Example - No Policy Component
<control-implementation>
<implemented-requirement uuid="uuid-value" control-id="ac-1">
<statement uuid="uuid-value" statement-id="ac-1_smt.a">
<by-component component-uuid="uuid-of-this-system" uuid="uuid-value">
<description>
<p>Describe how Part a is satisfied within the system.</p>
</description>
<link href="#uuid-of-policy-resource-in-back-matter" rel="policy" />
</by-component>
</statement>
</implemented-requirement>
</control-implementation>
<!-- back-matter -->
For the component approach, use the component representing the policy.
The link should be in the component, but may be added directly to the
by-component as well.
Representation: Component Approach Example
<system-implementation>
<!-- leveraged-authorization, user -->
<component uuid="uuid-value" type="policy">
<title>Access Control and Identity Management Policy</title>
<description>description: <p>An'This example component representingis a policy.</p>corporate </description>AC <linkpolicy href="#uuid-of-policy-resource-in-back-matter"used rel="policy"for />the <statussystem.'
state="operational"/>props:
</component>- </system-implementation>name: <control-implementation>implementation-point
<implemented-requirementvalue: uuid="uuid-value"external
class: corporate
links:
- href: '#11111111-2222-4000-8000-001000000005'
rel: attachment
status:
state: operational
control-id="implementation:
implemented-requirements:
- uuid: 11111111-2222-4000-8000-012000010000
control-id: ac-1">1
<statementstatements:
uuid="uuid-value"- statement-id="id: ac-1_smt.a">a
<uuid: 11111111-2222-4000-8000-012000010100
by-componentcomponents:
- component-uuid="uuid-of-policy-component"uuid: uuid="uuid-value">11111111-2222-4000-8000-009000600001
<description>uuid: <p>11111111-2222-4000-8000-012000010102
description: Describe how this policy satisfies Partpart a.</p>
</description>implementation-status:
</by-component>state: </statement>implemented
</implemented-requirement>responsible-roles:
</control-implementation>
<!-- back-matterrole-id: information-system-security-officer
party-uuids:
-->
11111111-2222-4000-8000-004000000008
Forremarks: eitherThis example above,is the policy\"policy\" mustcomponent, bewhich presentrepresents asthe aAccess resourceinand Identity Management Policy.
back-matter.
matter:
Inresources:
Back- Matter
uuid: <back-matter>11111111-2222-4000-8000-001000000005
<resourcetitle: uuid="uuid-value">
<title>Access Control and Identity Management Policy<
description: A single policy that addresses both the AC and IA families.
props:
- name: type
value: policy
- name: published
value: '2023-01-01T00:00:00Z'
- name: version
value: '1.2'
rlinks:
- href: ./title>
<rlinkattachments/policies/sample_AC_and_IA_policy.pdf
media-type="type: application/pdf" href="./documents/policies/sample_policy.pdf" />
<base64 filename="sample_policy.pdf" media-type="application/pdf">00000000</base64>
</resource>
</back-matter>pdf