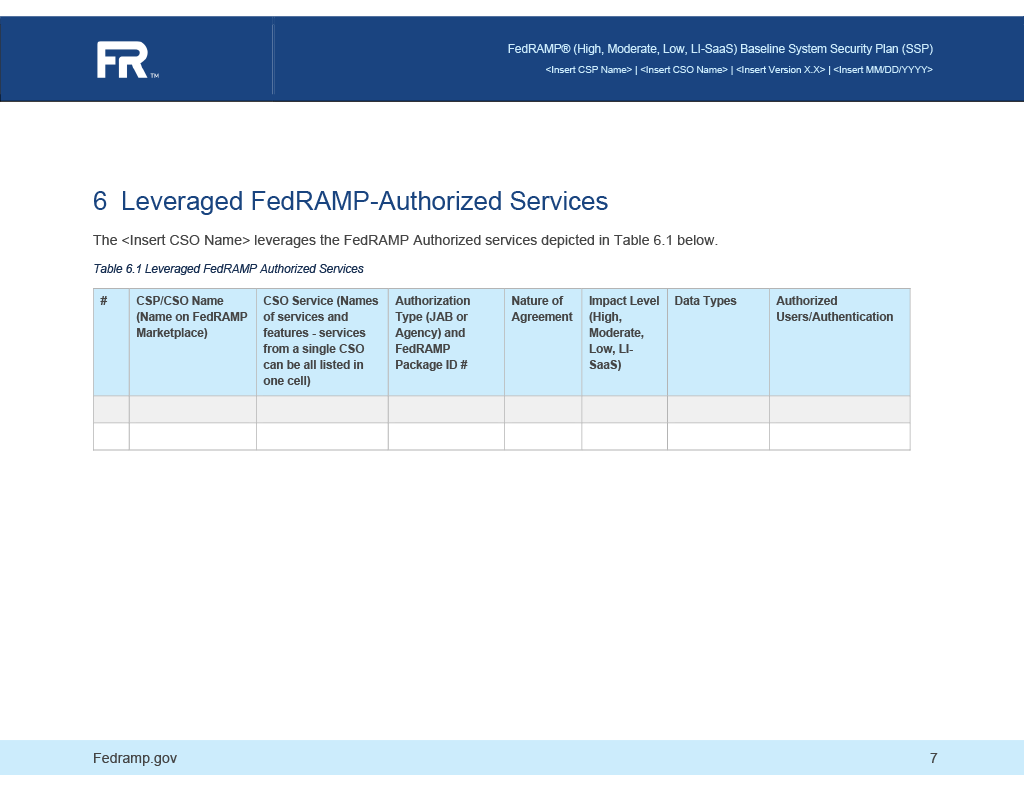
6. Leveraged FedRAMP-Authorized Services
The leveraged FedRAMP-Authorized services table is used to list both underlying leveraged authorizations, such as a SaaS running on an IaaS, and use of external cloud services with FedRAMP authorizations, such as a FedRAMP-authorized third party identity management service.
For each row in Table 6.1 there must be:
- a
partiesentry - a
leveraged-authorizationsentry - a
componentsentry
parties Entry
A parties entry to indicate the organizaiton that owns the leveraged system or external service
system-security-plan:
metadata:
parties:
- uuid: 22222222-2222-4000-8000-004000000001
type: organization
name: Leveraged System Provider's Name
short-name: LSPN
leveraged-authorizations Entry
- a
uuid - a
titlewith the name of the system or service exactly as it appears in the FedRAMP Marketplace - a
propsentry with:nameset topackage-idnsset tohttp://fedramp.gov/ns/oscalvalueset to the package ID exactly as it appears in the FedRAMP Marketplace
- a
propsentry with:nameset tosecurity-sensitivity-levelnsset tohttp://fedramp.gov/ns/oscalvalueset tofips-199-low,fips-199-modareteorfips-199-highconsistent with the FedRAMP Marketplace Information
- a
party-uuidwith the UUID of thepartiesentry above - a
date-authorizedwith the date listed in the FedRAMP Marketplace, expressed in OSCALdateformat.
FedRAMP Extensions
FedRAMP Extensions are defined when there is no way to represent required information using core OSCAL. They are depicted as propterties (props entries) with a namespace (ns) value set to http://fedramp.gov/ns/oscal. Without the namespace, these properties may be ignored or flagged as invalid.
system-security-plan:
system-implementation:
leveraged-authorization:
- uuid: 11111111-2222-4000-8000-019000000001
title: CSO Name
props:
- name: package-id
ns: http://fedramp.gov/ns/oscal
value: F9999999999
- name: security-sensitivity-level
ns: http://fedramp.gov/ns/oscal
value: fips-199-high
party-uuid: 22222222-2222-4000-8000-004000000001
date-authorized: '2015-01-01'
Allowed Values
The FedRAMP extension security-sensitivity-level:
fips-199-highfips-199-moderatefips-199-low
components Entry
The components entry must include:
-
a
uuid -
a
typeset tosystem -
a
titleset to the name of the leveraged system -
a
descriptionof the system. This is a core OSCAL requirement. FedRAMP has no specific requirement for the content of this field. -
a
propsentry with:nameset toleveraged-authorization-uuidvalueset to the UUID of theleveraged-authorizationentry above
-
a
propsentry with:nameset tonature-of-agreementnsset tohttp://fedramp.gov/ns/oscalvalueset tosla,contract[needs more definition]
-
a
propsentry with:nameset toauthentication-methodnsset tohttp://fedramp.gov/ns/oscalvalueset to the package ID exactly as it appears in the FedRAMP Marketplace
-
One
propsentry for each "Data Type":nameset toinformation-typensset tohttp://fedramp.gov/ns/oscalvalueset to the NIST SP 800-60 Volume 2 information IDclassset toincomingoroutgoing- If the same information type is exchanged in both directions, there must be one
propsentry for incoming and a separate props entry for outgoing.
-
The
statusassembly with thestatefield set tooperational- For FedRAMP the value must always be operational; however, this is a required OSCAL field and cannot be omitted.
-
One or more
responsible-rolesentries:- Identify the Provider (Required):
role-idset toprovider(ensuremetadatahas arolesentry withidset toprovider)- a
party-uuidsentry with the UUID of thepartiesentry defined above.
- Authorized Users: One entry per authorized user type:
role-id- Use OSCAL-defined canonical values where appropriate.
- If no canonoical value exists, create an appropriate value that conforms with the OSCAL
tokendata type. - The value must also exist in the
metadata/rolesentries.
- Identify the Provider (Required):
OSCAL Representation
system-security-plan:
system-implementation:
component:
- uuid: 11111111-2222-4000-8000-009000100001
type: system
title: Leveraged Authorized System
description: Briefly describe the leveraged system.
props:
- name: leveraged-authorization-uuid
value: 11111111-2222-4000-8000-019000000001
- name: nature-of-agreement
ns: http://fedramp.gov/ns/oscal
value: sla
- name: authentication-method
ns: http://fedramp.gov/ns/oscal
value: 'yes'
- name: information-type
ns: http://fedramp.gov/ns/oscal
value: C.3.5.1
class: incoming
- name: information-type
ns: http://fedramp.gov/ns/oscal
value: C.3.5.8
class: outgoing
status:
state: operational
responsible-roles:
- role-id: provider
party-uuids:
- 11111111-2222-4000-8000-c0040000000a
- role-id: asset-administrator
party-uuids:
- 11111111-2222-4000-8000-c0040000000a
FedRAMP Marketplace Information Matching
Information about Leveraged FedRAMP Authorized Services must match the content in the FedRAMP Marketplace. GSA updates a JSON file nightly that is used to render the FedRAMP Marketplace data.
| OSCAL Field | GSA Field |
|---|---|
| CSP Name | /data/Providers/[#]/Cloud_Service_Provider_Name |
| CSO Name | /data/Providers/[#]/Cloud_Service_Provider_Package |
| Package ID | /data/Providers/[#]/Package_ID |
| Authorization Date | /data/Providers/[#]/Original_Authorization_Date |
| Impact Level | /data/Providers/[#]/Impact_Level |
IMPORTANT FOR LEVERAGED SYSTEMS:
While a leveraged system has no need to represent content here, its SSP SHOULD include special inheritance and responsibility information in the individual controls. See the Response: Identifying Inheritable Controls and Customer Responsibilities section for more information.

We need to fix the link in the "Important for Leveraged Systems" callout once the controls section is complete and the location is not likely to change again.
No comments to display
No comments to display